FortiNDR: Next-Generation Network Threat Detection and Response
When we look at the evolution of cyber security architectures, we see that the main line of security has long been formed by Firewall, IPS, and later EDR solutions. However, today the techniques used by attackers have taken on a more invisible, more behavior-focused, and often fileless form that goes beyond these classical layers. This transformation makes it clear that signature-based or endpoint-focused security approaches alone are no longer sufficient.
It is precisely at this point that FortiNDR (Network Detection & Response), one of Fortinet’s most technically capable solutions, comes into play. Although it does not yet have widespread popular awareness in the market, it is winking at its competitors particularly in advanced threat hunting and behavioral analysis.

What is FortiNDR? Not Just Detection, but a Decision Mechanism
FortiNDR is a network detection and response platform that performs deep analysis of network traffic and is built on artificial intelligence (AI) and machine learning (ML). Unlike traditional NIDS/NIPS approaches, beyond known signatures, it models network behaviors and learns to distinguish between normal and unusual activities. (This learning aspect is, in my opinion, especially critical for constantly changing environments.) This makes it possible to detect zero-day attacks and fileless threats.
Modern attack techniques now use Living-off-the-Land methods (abuse of legitimate tools) instead of direct delivery of malicious files, conduct C2 communications within encrypted traffic, and target systems that fall outside EDR visibility (IoT/OT). FortiNDR can close these blind spots by providing a behavioral answer to the question of what is really happening on the network. It also offers a flexible deployment architecture with options such as Standalone Mode and Sensor Mode. Standalone Mode enables analysis from a single center, while Sensor Mode (Center Architecture) allows centralized analysis (Center node) by collecting data from distributed sensors.
It is clear that the question of where visibility begins and where it ends always remains on the table in distributed structures. This architecture offers good flexibility especially for multi-location enterprise environments and MSSP (Managed Security Service Providers) environments.
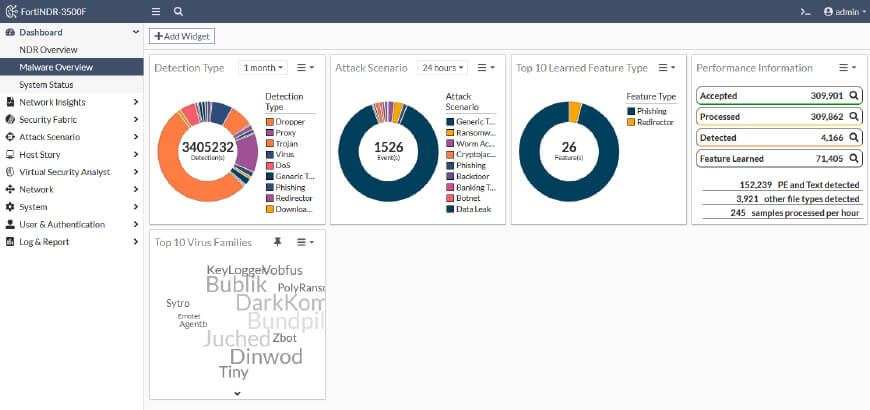
Malware Analysis in Seconds
The most striking feature that distinguishes FortiNDR from other NDR solutions on the market is that it can complete malware analysis in less than a second most of the time, and within a few seconds depending on the environment. While reading this, the question of "is it the same when traffic is heavy?" may come to mind; in the second part of our series, we will conduct hands-on tests with different environments to measure this capability. While many competitor products forward traffic to the cloud for analysis and wait for a response, FortiNDR produces instant decisions about malicious files via its built-in ML engine. Naturally, the attacker’s lateral spread is expected to be cut off quickly.
Virtual Security Analyst
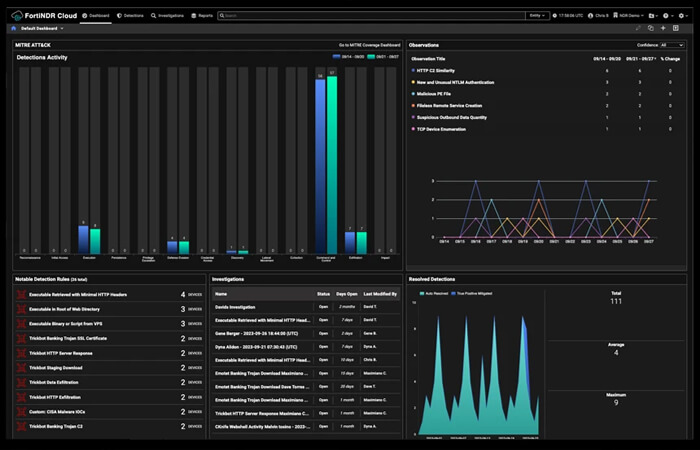
This module within FortiNDR performs in seconds a job that a security analyst would otherwise spend hours on. While the most time-consuming part of operations is piecing things together one by one, this module aims to reduce that burden. The core functions provided by the module are as follows:
Express Malware: When suspicious files are uploaded manually, it produces results through instant hash analysis and behavioral classification. It is a practical method especially for "can we take a look at this file" requests.
Outbreak Search (Retrospective Threat Hunting): Reports retrospectively whether a specific IoC (Indicator of Compromise) or hash has been observed on the network in the past, which hosts have been affected, and the initial entry point of the attack. While searching for "where did it start" after an incident is a long and difficult process, it appears our work will get easier here.
Malware Big Picture: Presents an attack not as a single alarm but as a "story." We have all experienced the difficulty of searching for something within a pile of alarms. The approach of showing the bigger picture here is quite important.
NDR Muting & Static Filter: "Mute" and "allow-list" features are available for maintenance work or trusted traffic patterns. Operating a healthy NDR without false-positive management is hardly possible, and the muting feature offers a method that simplifies this process.
ML Discovery & Config: The machine-learning engine is customizable. The system can label as anomalies anything that falls outside the normal profile it has learned.
Enforcement Profile (Automation): Automatic action can be taken for detected threats. With Ban/Unban logic, suspicious IPs can be automatically quarantined via FortiGate, and in the event of a false positive, this action can be easily reverted.
Native Integration with the Fortinet Security Fabric
While many NDR solutions on the market remain only as a monitoring layer, FortiNDR sits directly at the center of the Security Fabric architecture:
FortiGate: Stops detected threats with quarantine or blocking mechanisms.
FortiNAC: Isolates the network access of suspicious devices.
FortiSIEM & FortiSOAR: Enriches security events and triggers automated response processes (playbooks).
Conclusion and Evaluation
Today’s security architecture should be built on the EDR + NDR + SIEM tripod. We can say that the era of catching things with a single product is now over. NDR can provide the network intelligence that EDR cannot see at the endpoint and SIEM cannot see in correlation. Especially in IoT and OT (Industrial) networks where agents cannot be installed, due to its ability to perform industrial protocol analysis, FortiNDR comes with a level of visibility that can directly compete with dedicated OT security solutions.
To conclude, we can say that FortiNDR is not just a monitoring tool but a comprehensive platform that, with AI assistance, shows the current state of the network, diagnoses attacker movements within milliseconds, and can instantly turn this diagnosis into a defensive action.
In this article we covered the core philosophy and architectural advantages of FortiNDR. In the next part of our series, we will go deeper into the technical capabilities of the FortiNDR product, examining the interface menus one by one and addressing configuration details and operational use scenarios in detail. There we will particularly evaluate together how tuning, alarm management, and integration topics are operated in practice. See you in our next series
Ülkü YAŞAR
Cyber Security Engineer